Computer Networking > QUESTIONS & ANSWERS > CEH Exam (Latest update), 2024 - 2025, Questions and answers with Complete Solutions (All)
CEH Exam (Latest update), 2024 - 2025, Questions and answers with Complete Solutions
Document Content and Description Below
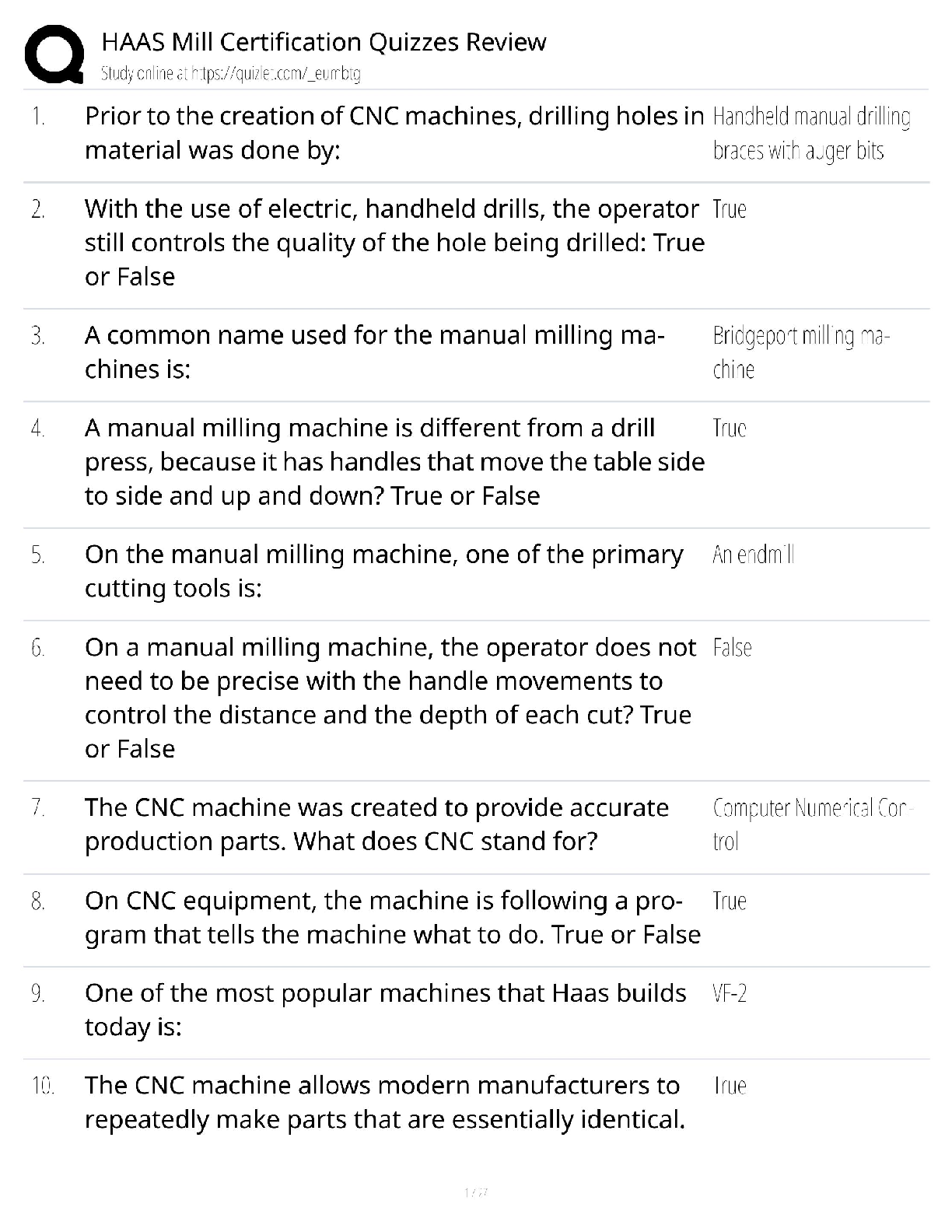
Which of the following countermeasure can specifically protect against both the MAC Flood and MAC Spoofing attacks? A. Configure Port Security on the switch B. Configure Port Recon on the switch ... C. Configure Switch Mapping D. Configure Multiple Recognition on the switch - ✔✔- A. Configure Port Security on the switch Jimmy, an attacker, knows that he can take advantage of poorly designed input validation routines to create or alter SQL commands to gain access to private data or execute commands in the database. What technique does Jimmy use to compromise a database? A. Jimmy can submit user input that executes an operating system command to compromise a target system B. Jimmy can gain control of system to flood the target system with requests,preventing legitimate users from gaining access C. Jimmy can utilize an incorrect configuration that leads to access with higher-than expected privilege of the database D. Jimmy can utilize this particular database threat that is an SQL injection technique to penetrate [Show More]
Last updated: 1 year ago
Preview 5 out of 350 pages

Loading document previews ...
Buy this document to get the full access instantly
Instant Download Access after purchase
Buy NowInstant download
We Accept:
Reviews( 0 )
$8.00
Can't find what you want? Try our AI powered Search
Document information
Connected school, study & course
About the document
Uploaded On
Dec 01, 2024
Number of pages
350
Written in
All
Additional information
This document has been written for:
Uploaded
Dec 01, 2024
Downloads
0
Views
96