Information Security (EXAM1, Chapter 4)
The ISSP is a plan which sets out the requirements that must be met by the information security
blueprint or framework. - ✔✔false
The complete details of ISO/IEC 27002 are widel
...
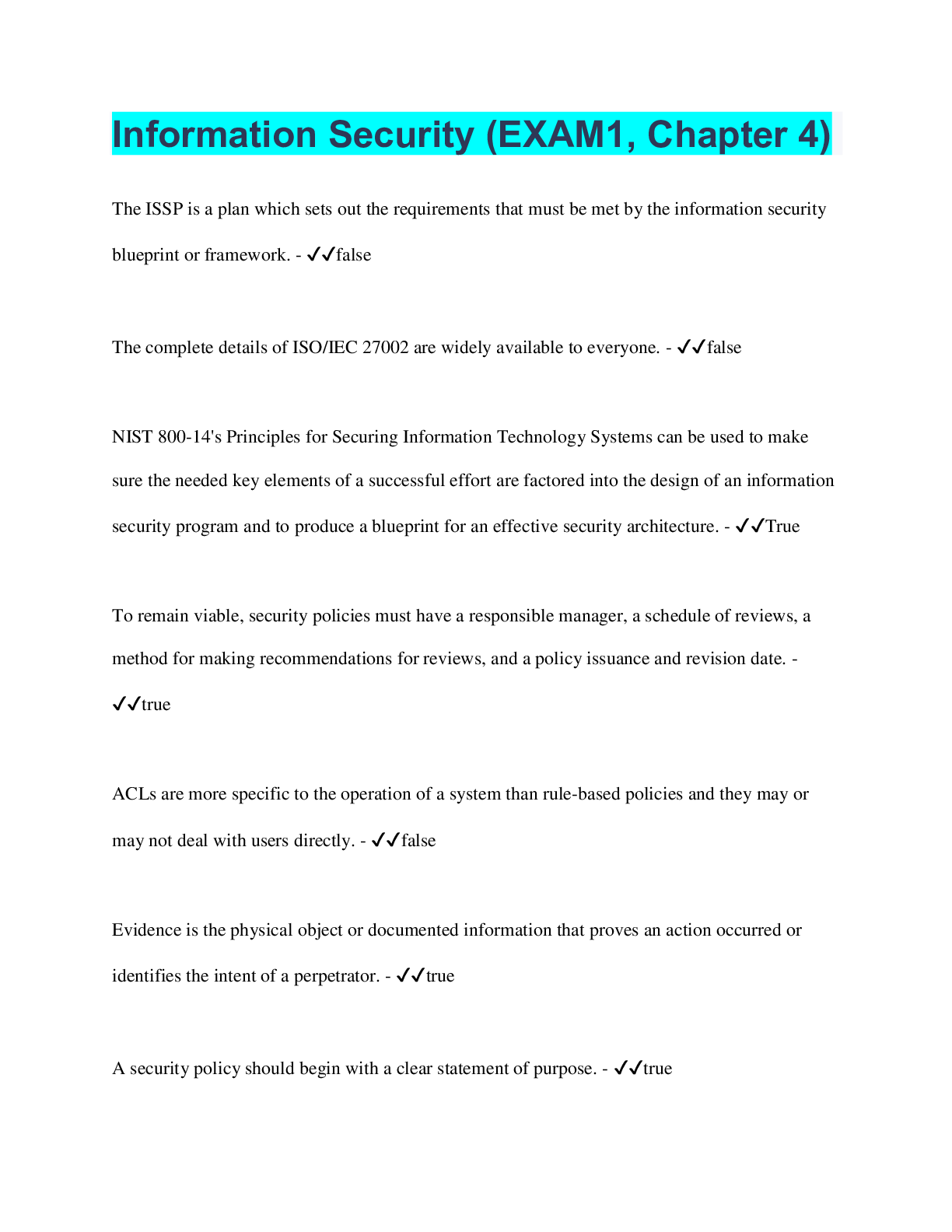
Information Security (EXAM1, Chapter 4)
The ISSP is a plan which sets out the requirements that must be met by the information security
blueprint or framework. - ✔✔false
The complete details of ISO/IEC 27002 are widely available to everyone. - ✔✔false
NIST 800-14's Principles for Securing Information Technology Systems can be used to make
sure the needed key elements of a successful effort are factored into the design of an information
security program and to produce a blueprint for an effective security architecture. - ✔✔True
To remain viable, security policies must have a responsible manager, a schedule of reviews, a
method for making recommendations for reviews, and a policy issuance and revision date. -
✔✔true
ACLs are more specific to the operation of a system than rule-based policies and they may or
may not deal with users directly. - ✔✔false
Evidence is the physical object or documented information that proves an action occurred or
identifies the intent of a perpetrator. - ✔✔true
A security policy should begin with a clear statement of purpose. - ✔✔true
The security framework is a more detailed version of the security blueprint. - ✔✔false
Systems-specific security policies are organizational policies that provide detailed, targeted
guidance to instruct all members of the organization in the use of a resource, such as one of its
processes or technologies. - ✔✔false
One of the basic tenets of security architectures is the layered implementation of security, which
is called defense in redundancy. - ✔✔false
To remain viable, security policies must have a responsible individual, a schedule of reviews, a
method for making recommendations for reviews, and policy issuance and planned revision
dates. - ✔✔true
Managerial controls set the direction and scope of the security process and provide detailed
instructions for its conduct. - ✔✔true
In 2016, NIST published a new Federal Master Cybersecurity Framework to create a mandatory
framework for managing cybersecurity risk for the delivery of critical infrastructure services at
every organization in the United States, based on vendor-specific technologies. - ✔✔false
Some policies may also need a(n) sunset clause indicating their expiration date. - ✔✔true
Guidelines are detailed statements of what must be done to comply with policy. - ✔✔false
A(n) sequential roster is activated as the first person calls a few people on the roster, who in turn
call a few other people. - ✔✔false
NIST responded to a mandate and created a voluntary Risk Management Framework that
provides an effective approach
to manage cybersecurity risks. - ✔✔true
You can create a single, comprehensive ISSP document covering all information security issues.
- ✔✔true
The Computer Security Resource Center at NIST provides several useful documents free of
charge in its special publications area - ✔✔true
A policy should state that if employees violate a company policy or any law using company
technologies, the company will protect them, and the company is liable for the employee's
actions. - ✔✔false
A standard is a written instruction provided by management that informs employees and others
in the workplace about proper behavior. - ✔✔false
Good security programs begin and end with policy. - ✔✔true
Every member of the organization's InfoSec department must have a formal degree or
certification in information security. - ✔✔false
An attack, breach of policy, or other incident always constitutes a violation of law, requiring
notification of law enforcement. - ✔✔false
Security training provides detailed information and hands-on instruction to employees to prepare
them to perform their duties securely. - ✔✔true
The stated purpose of ISO/IEC 27002 is to offer guidelines and voluntary directions for
information security management. - ✔✔true
A cold site provides many of the same services and options of a hot site, but at a lower cost. -
✔✔false
A hard drive feature known as "hot swap" is a RAID implementation (typically referred to as
RAID Level 1) in which the computer records all data to twin drives simultaneously, providing a
backup if the primary drive fails. - ✔✔false
A disaster recovery plan shows the organization's intended efforts to restore operations at the
original site in the aftermath of a disaster. - ✔✔true
A(n) disaster is any adverse event that could result in loss of an information asset or assets, but
does not currently threaten the viability of the entire organization. - ✔✔false
The operational plan documents the organization's intended long-term direction and efforts for
the next several years. - ✔✔false
The ISO/IEC 27000 series is derived from an earlier standard, BS7799. - ✔✔true
Failure to develop an information security system based on the organization's mission, vision,
and culture guarantees the failure of the information security program. - ✔✔true
Within security perimeters the organization can establish security redundancies, each with
differing levels of security, between which traffic must be screened. - ✔✔false
A managerial guidance SysSP document is created by the IT experts in a company to guide
management in the implementation and configuration of technology. - ✔✔false
A(n) DR plan ensures that critical business functions continue if a catastrophic incident or
disaster occurs. - ✔✔false
The security model is the basis for the design, selection, and implementation of all security
program elements, including policy implementation and ongoing policy and program
management. - ✔✔false
Database shadowing duplicates data in real-time data storage, but does not back up the databases
at the remote site. - ✔✔false
To achieve defense in depth, an organization must establish multiple layers of security controls
and safeguards. - ✔✔true
The policy administrator is responsible for the creation, revision, distribution, and storage of the
policy. - ✔✔true
NIST Special Publication 800-18 Rev. 1, The Guide for Developing Security Plans for Federal
Information Systems, includes templates for major application security plans, and provides
detailed methods for assessing, designing, and implementing controls and plans for applications
of varying size. - ✔✔true
Technical controls are the tactical and technical implementations of security in the organization.
- ✔✔true
The recovery point objective (RPO) is the point in time prior to a disruption or system outage to
which mission/business process data can be recovered after an outage. - ✔✔true
A(n) alarming event is an event with negative consequences that could threaten the
organization's information assets or operations. - ✔✔false
A(n) strategic information security policy is also known as a general security policy, and sets the
strategic
direction, scope, and tone for all security efforts - ✔✔false
Disaster recovery personnel must know their roles without supporting documentation, which is a
function of preparation, training, and rehearsal. - ✔✔true
A(n) capability table specifies which subjects and objects users or groups can access. - ✔✔true
The key components of the security perimeter include firewalls, DMZs (demilitarized zones),
Web servers, and IDPSs. - ✔✔false
Each policy should contain procedures and a timetable for periodic review. - ✔✔true
The global information security community has universally agreed with the justification for the
code of practices as identified in the ISO/IEC 17799. - ✔✔false
[Show More]


.png)