Information Technology > QUESTIONS & ANSWERS > Cybersecurity Analyst Quiz (FedVTE) Questions and Answers [Verified Solutions] (All)
Cybersecurity Analyst Quiz (FedVTE) Questions and Answers [Verified Solutions]
Document Content and Description Below
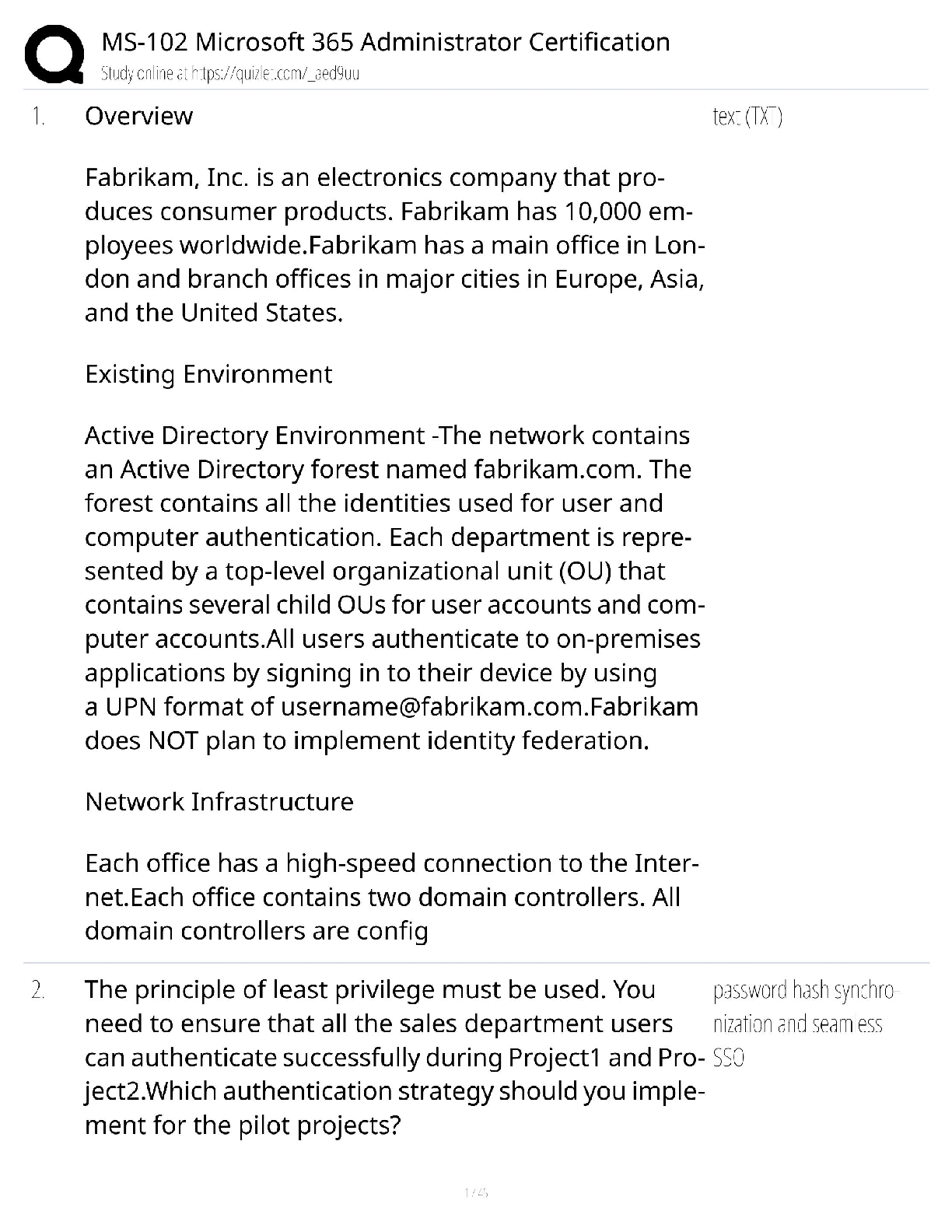
Cybersecurity Analyst Quiz (FedVTE) Questions and Answers [Verified Solutions] Which of the following is a common environmental reconnaissance task that is performed to help gain insight on how an ... organization's networked systems are connected, or mapping the network? ✔✔Topology Discovery If an unexpected issue occurred during an application installation on a Windows system, which of the following event log categories would be best to reference for troubleshooting? ✔✔Not System or Security. Maybe Setup The federal version of certification and accreditation guidance that applies to departments and agencies within the Department of Defense is: ✔✔DIACAP Which security mechanism can social engineering help bypass? ✔✔A. Intrusion Detection Systems B. Firewalls C. Domain Security Policies (No) D. All of the Above E. None of the Above Which type of intrusion detection may terminate processes or redirect traffic upon detection of a possible intrusion? ✔✔Active Which of the following is a potential consequence of not limiting or protecting communications during an incident? ✔✔All of the Above (Customer confidence may be negatively impacted, Competitors may recognize weakness or advantage, Media may include information not intended for release) Which one of the following can be managed through group policies (GPO)? ✔✔All the Above (Authentication settings, Software installation and update, IPsec connections) What is used to record the order in which evidence was handled, by whom, and the nature of the evidence handling? ✔✔Chain of custody The procedure of developing controls as vulnerabilities are discovered to keep them from being exploited is known as: ✔✔A. Change Control Management B. Compensating Control Development C. Vulnerability Control Patch D. Remediation Control Development (No) Which of the following are Windows event severity levels: ✔✔error, warning, information Which of the following intrusion detection systems uses statistical analysis to detect intrusions? ✔✔Anomaly Which one of the following is a use for Network Flow Data? ✔✔All of the Above (Attack identification and attribution such as DoS detection, Traffic engineering such as a host analysis, Accounting to cross verify other sources) Which of the following is an attacker most likely to use to attempt to view packets containing data in clear text? ✔✔Wireshark Packets from a computer outside the network are b [Show More]
Last updated: 2 years ago
Preview 1 out of 9 pages
![Preview image of Cybersecurity Analyst Quiz (FedVTE) Questions and Answers [Verified Solutions] document](https://www.scholarfriends.com/storage/Cybersecurity Analyst Quiz (1).png)
Buy this document to get the full access instantly
Instant Download Access after purchase
Buy NowInstant download
We Accept:
Also available in bundle (1)
Click Below to Access Bundle(s)
.png)
[SOLVED] FedVTE BUNDLED EXAMS QUESTIONS AND ANSWERS WITH COMPLETE AND VERIFIED SOLUTIONS
[SOLVED] FedVTE BUNDLED EXAMS QUESTIONS AND ANSWERS WITH COMPLETE AND VERIFIED SOLUTIONS
By Nutmegs 2 years ago
$20
20
Reviews( 0 )
$10.00
Can't find what you want? Try our AI powered Search
Document information
Connected school, study & course
About the document
Uploaded On
Jan 02, 2023
Number of pages
9
Written in
All
Additional information
This document has been written for:
Uploaded
Jan 02, 2023
Downloads
0
Views
159







.png)