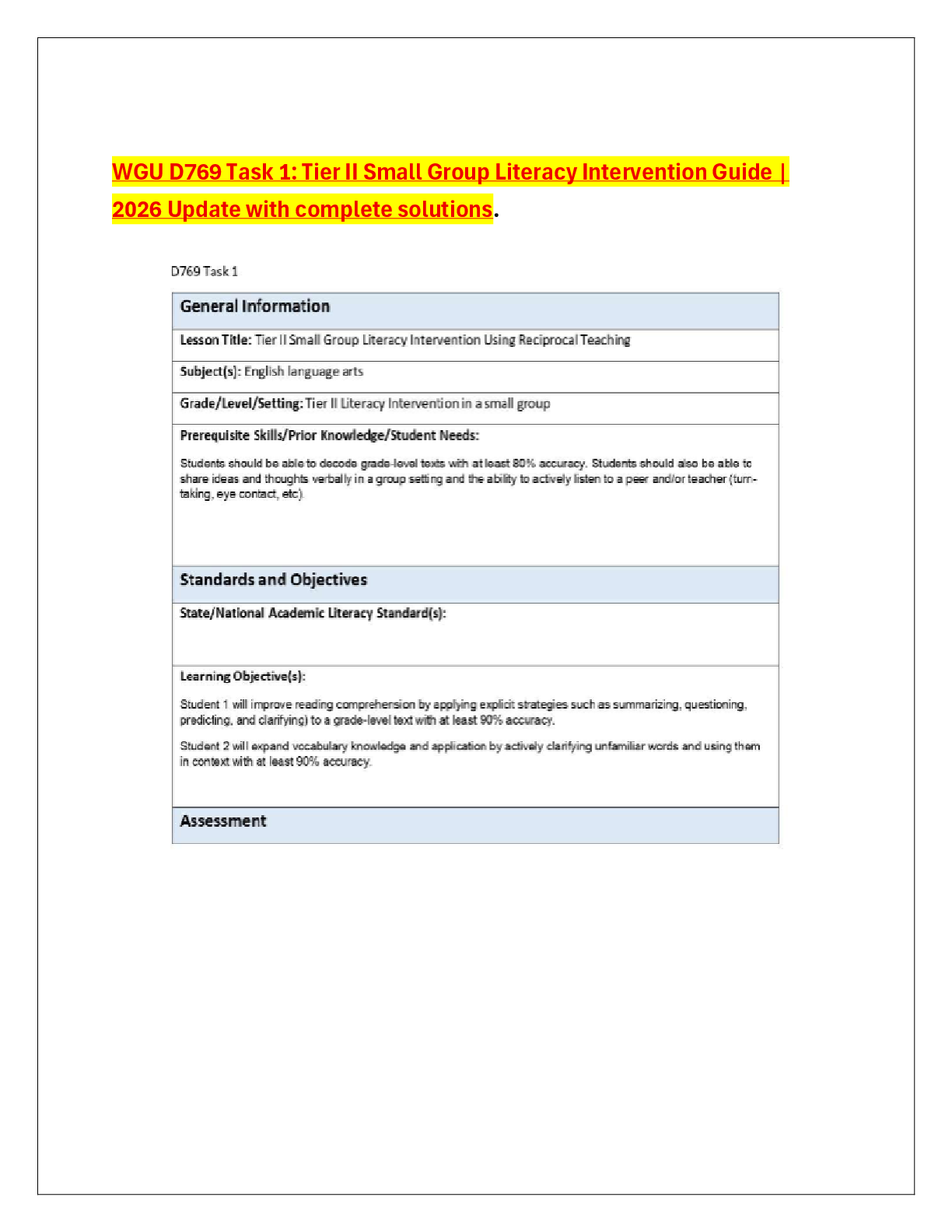
WGU D769 Task 1: Tier II Small Group Literacy Intervention Guide | 2026 Update with complete solutions.
Business > CASE STUDY > security standard_Task1.docx Security Policies and St (All)
Last updated: 3 years ago
Preview 1 out of 10 pages
Instant download

Buy this document to get the full access instantly
Instant Download Access after purchase
Buy NowInstant download
We Accept:
Can't find what you want? Try our AI powered Search
Connected school, study & course
About the document
Uploaded On
Sep 04, 2022
Number of pages
10
Written in
All
This document has been written for:
Uploaded
Sep 04, 2022
Downloads
0
Views
56
Scholarfriends.com Online Platform by Browsegrades Inc. 651N South Broad St, Middletown DE. United States.
We're available through e-mail, Twitter, and live chat.
FAQ
Questions? Leave a message!
Copyright © Scholarfriends · High quality services·