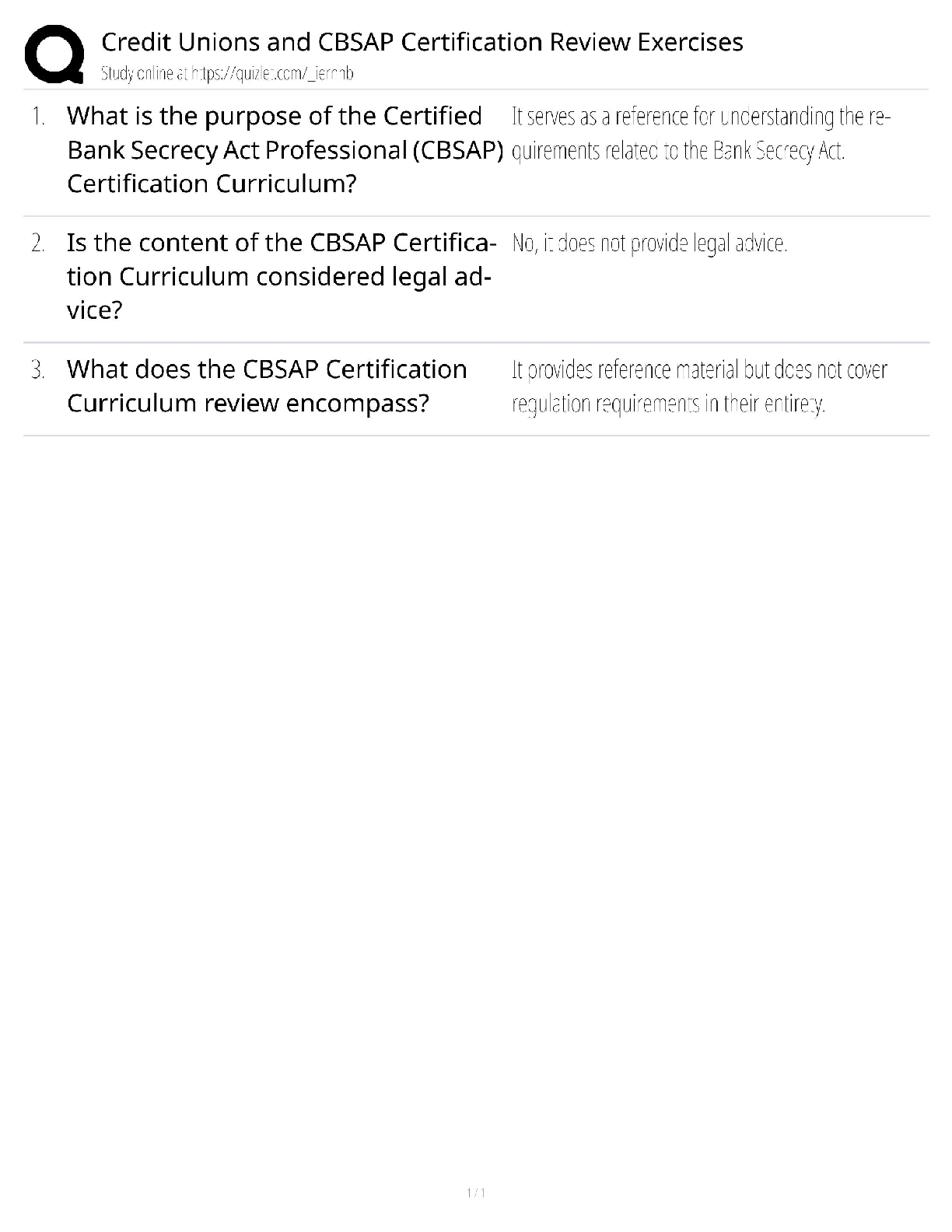
Microsoft Excel 2016 Certification / Formulas & Functions Guide / 2025 Update / Score 100%
$ 19.5
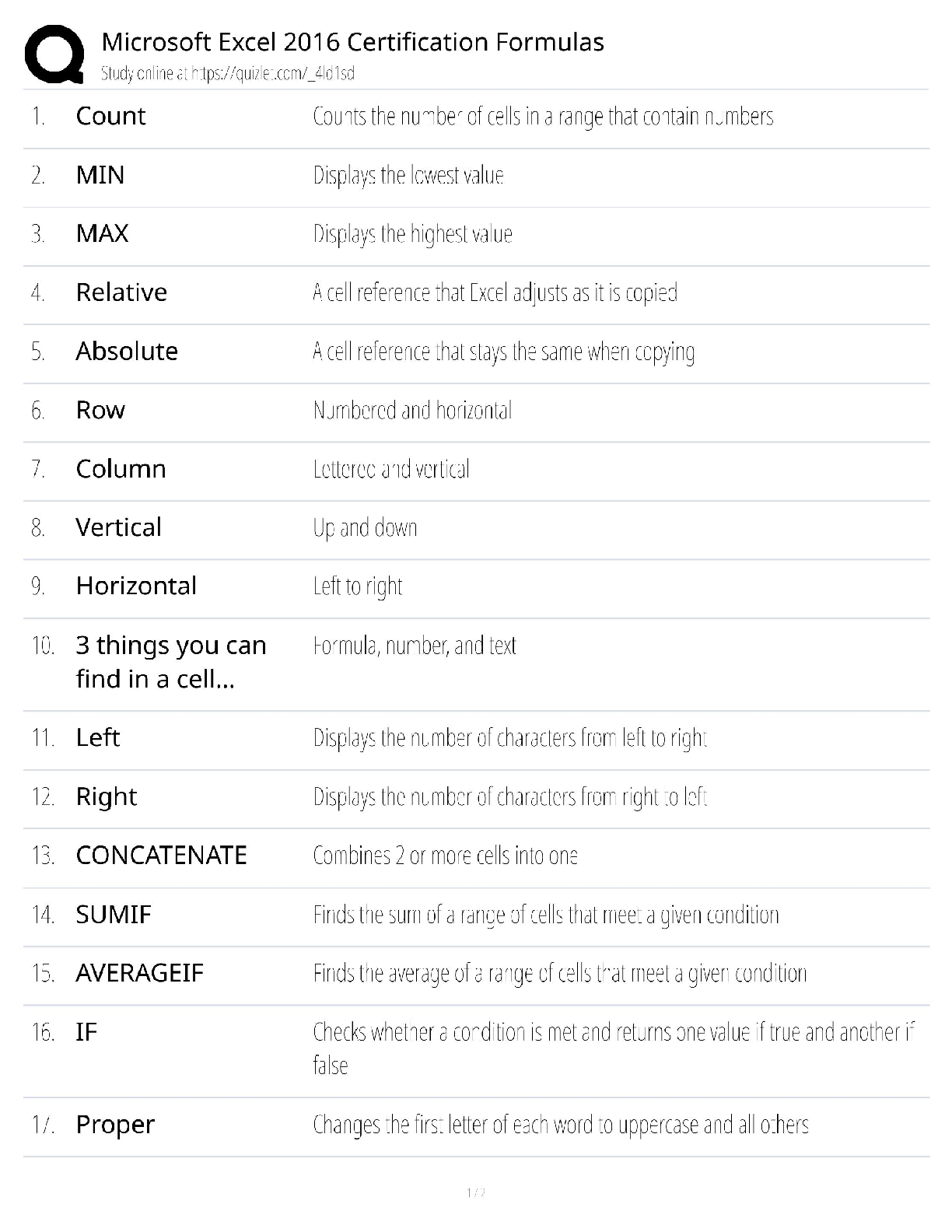
Test bank For Dosage Calculations A Multi-Method Approach 2nd Edition By Anthony Giangrasso, Dolores Shrimpton
.png)
.png)







.png)