
Multinational Business Finance 16th Edition Eiteman Stonehill Moffett Test Bank | Complete Solutions for All Chapters | Chapter 1-20
$ 19.5
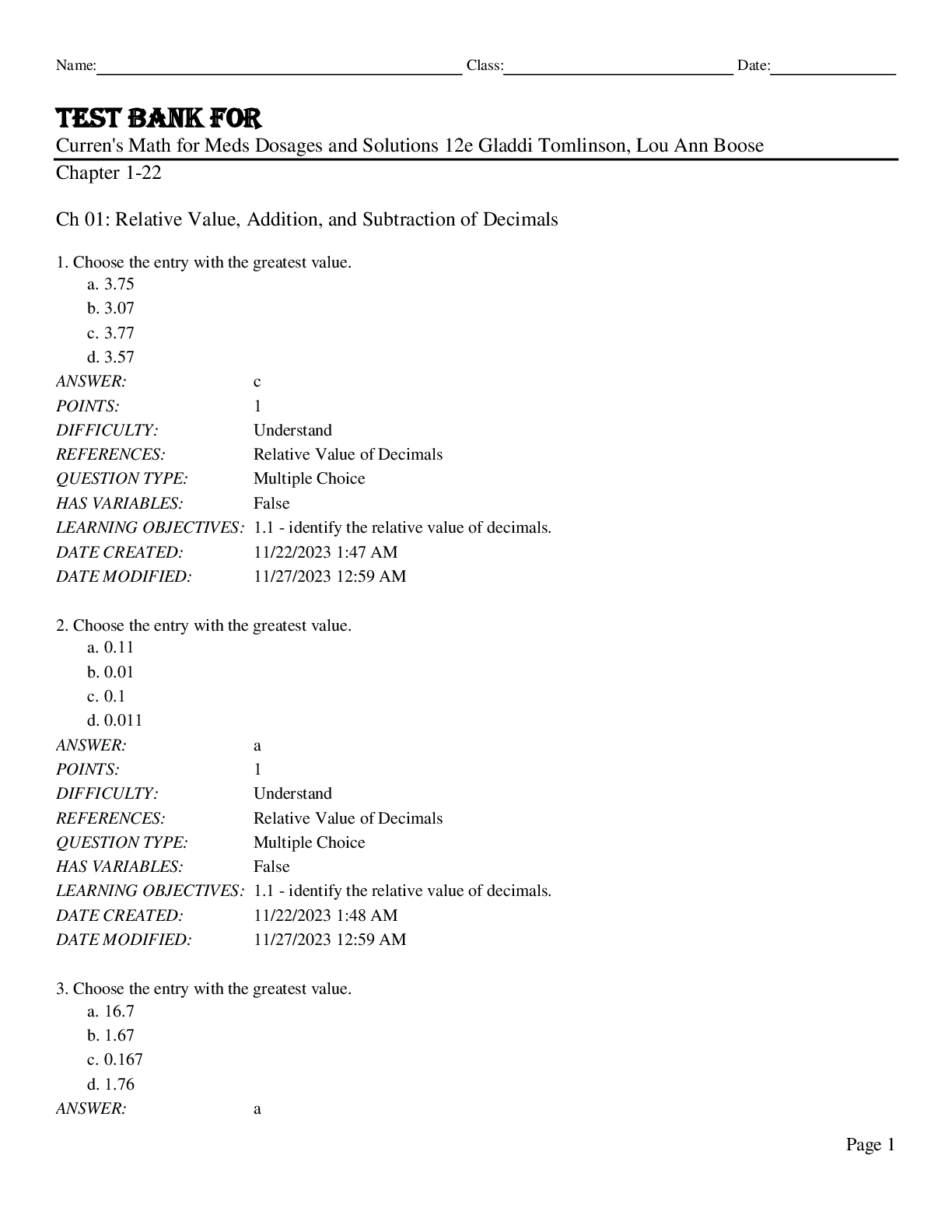
Test Bank for Curren's Math for Meds Dosages and Solutions 12th Edition by Gladdi Tomlinson, Lou Ann Boose











