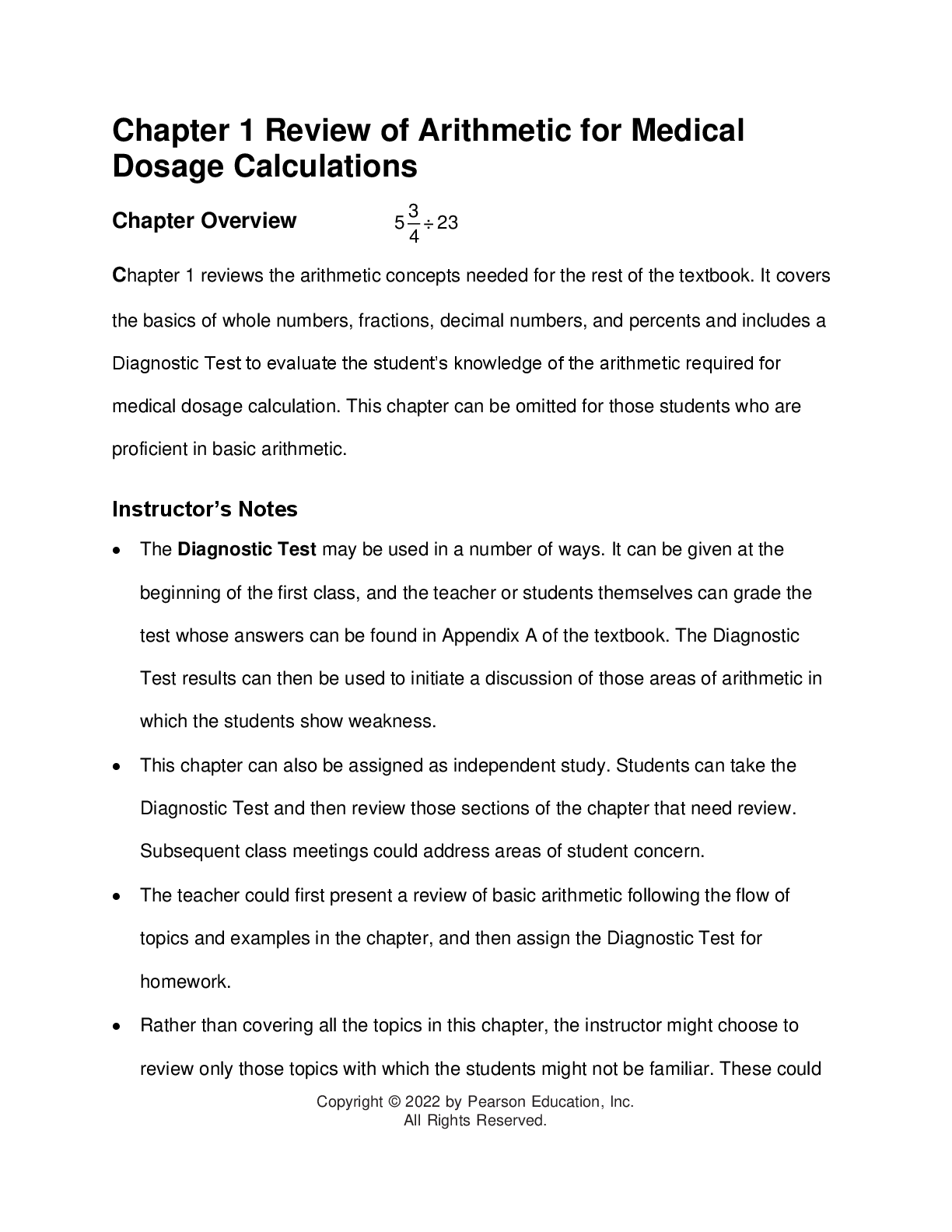
Solutions Manual for Medical Dosage Calculations A Dimensional Analysis Approach, Updated Edition, 11th Edition By June Olsen, Anthony Giangrasso, Dolores Shrimpton
$ 29
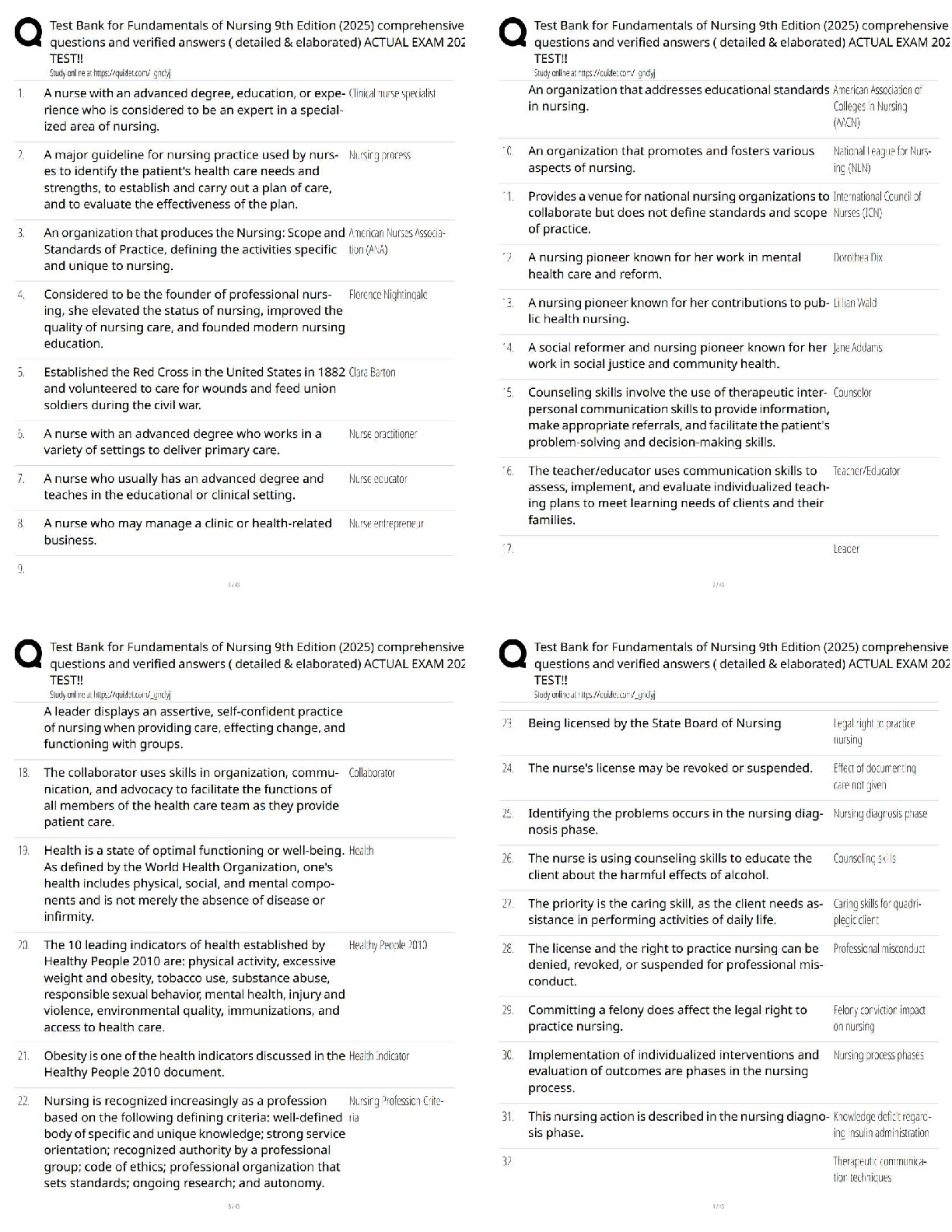
Taylor Fundamentals of Nursing 9th Edition Chapter 1 Quiz 2025 / Score 100% / Practice Questions, Test Bank & Study Guide
$ 20
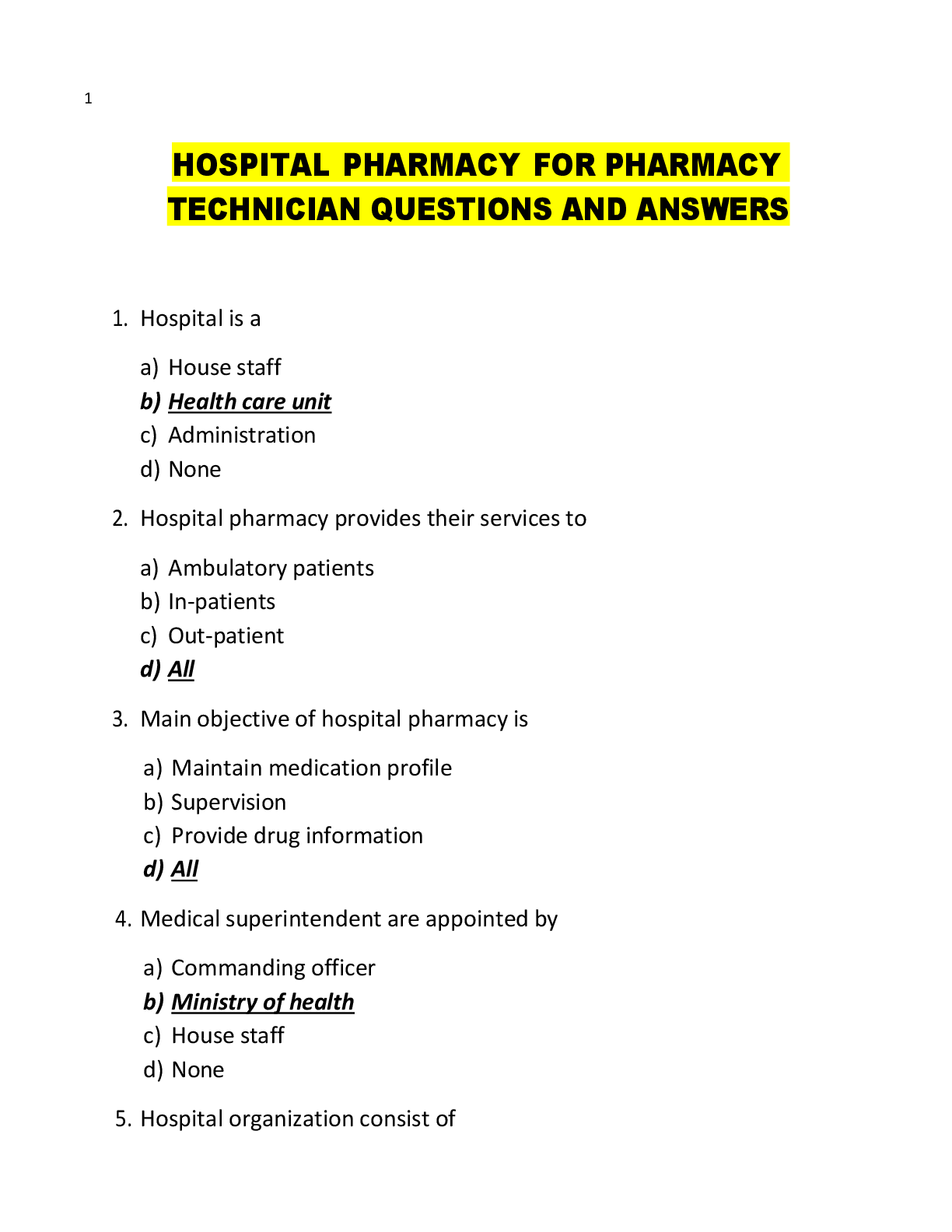
HOSPITAL PHARMACY FOR PHARMACY TECHNICIAN QUESTIONS AND ANSWERS
$ 16
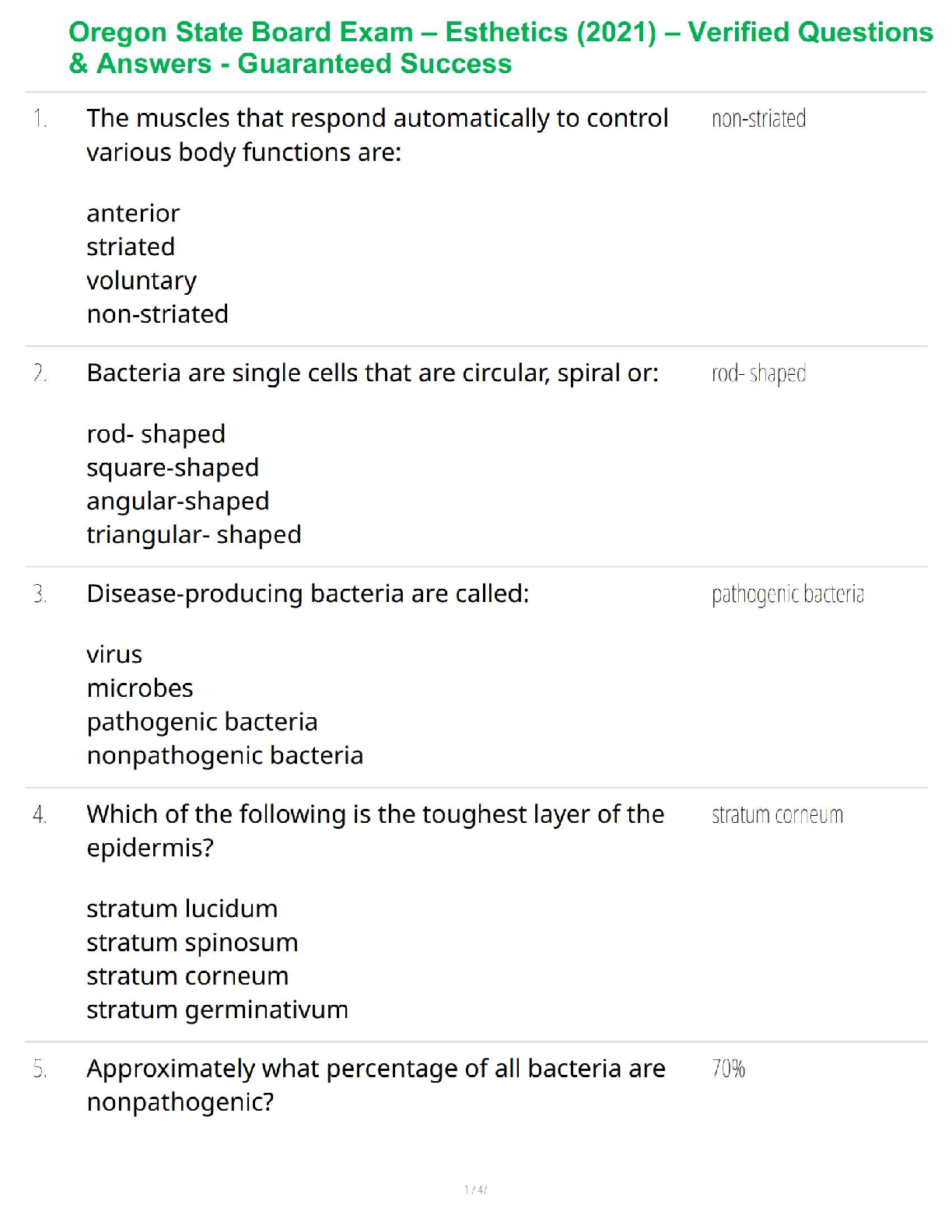
Oregon State Board Exam – Esthetics (2021) – Verified Questions & Answers - Guaranteed Success
$ 34

Pearson Edexcel International GCSE (4CN1/01R) Chinese Paper 1: Listening MARK SCHEME - May 2019
$ 5.5

Pearson Edexcel GCE In Spanish (9SP0) Paper 02 Written response to works and translation Mark Scheme (Results) November 2021
$ 6
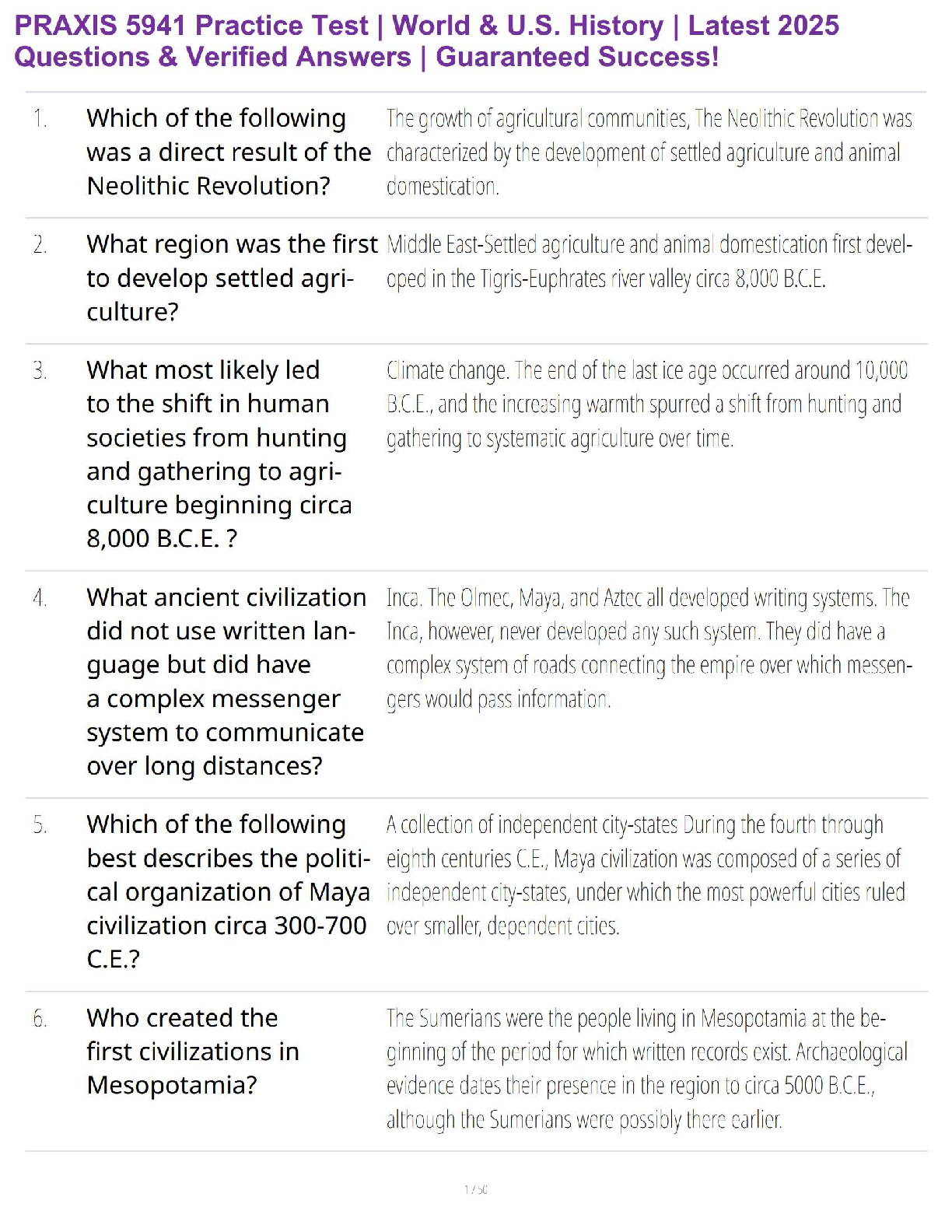
PRAXIS 5941 Practice Test – U.S. & World History Exam Prep with Verified Questions & Detailed Answers (2025 Edition)
$ 26.5
John Deere 240 and 250 Skid Steer Repair Technical Service Manual
$ 14.99

TEST BANK for Microbiology Fundamentals: A Clinical Approach 3rd Edition by Kelly Cowan, Heidi Smith
$ 23
WGU C909 Exam Questions with Correct Answers 2024-2025 (Latest Update Graded A+)
$ 12
D220 WGU Study Questions and Answers Test Bank (New Update) Verified Answers (GRADED A)
$ 12

Biology Notes Form 1 PDF _ Biology Form 1 Questions and Answers PDF.pdf
$ 7
eBook Research Methods Concepts and Connections, 1st Edition By Michael Passer(2)
$ 30
(Portage) CHM095 - Basic Lab Chemistry - Final Assessment Guide 2024-2025
$ 11
AQA GCSE Combined Science Trilogy _ Biology Paper 1
$ 15
.png)
Machine Learning for Financial Risk Management with Python: Algorithms for Modeling Risk 3rd Release by Abdullah Karasan
$ 19

Higher GCSE Biology B Twenty First Century Science J257/02: Depth in Biology (Foundation Tier) General Certificate of Secondary Education Mark Scheme for June 2023
$ 4

Pearson Edexcel Level 3 GCE Further Mathematics Advanced Subsidiary Further Mathematics options 25: Further Mechanics 1 (Part of options C, E, H and J) QUESTION PAPER 2022
$ 7

Adobe Photoshop Classroom in a Book, 2022 Release, 1st Edition, By Conrad Chavez, Andrew Faulkner [PDF] [eBook]
$ 25

A-level BIOLOGY Paper 2,. LATEST EXAMINABLE QUESTIONS.










